Got the screen, tore the phone open, took the old screen out (which broke as I was removing it), and started to install the new screen, but alas the new screen’s ribbon tore as I was putting it in. So I decided to probably do what any normal person would do and buy a new phone. In the mean time, I reassembled the phone and started on an epic quest to firstly get ADB running (cause apparently I had it disabled for some reason) and install a VNC server.
Since I had no way of interacting with the phone, I had no way of turning ADB on. Luckily, I had ClockWorkMod recovery installed. So I booted to recovery and was able to connect to the phone over ADB. Once I got a shell, I had to figure out a way to enable ADB for the main os. So I mounted all of the partitions in fstab and did some exploring. Ended up having to modify a few files in order to get ADB back. Here’s the full process:
mount -a
echo "1" > /data/property/persist.service.adb.enable
echo "adb" > /data/property/persist.sys.usb.config
/system/xbin/sqlite3 /data/data/com.android.providers.settings/databases/settings.db "update secure set value='1' where name='adb_enabled'"
sync
reboot
Sweet! ADB was enabled in the main os and there was much rejoicing. Now I had to install a VNC server. I ended up using droid VNC Server as other open source servers couldn’t open the framebuffer for some reason. I installed it using the Google Play Store’s ability to install apps on your phone remotely. I figured I could simply ADB in and activate the daemon using the shell, but as it turns out, the daemon gets extracted by the app to the data folder when you first run the app and hit the start button. Great. So after some googling I found out that you can start an app via the terminal using the am command. I was able to start the app using the following command:
am start -n org.onaips.vnc/.MainActivity
The app started, but doesn’t activate the server until you hit the “Start” button. Whats more, my screen was locked and wouldn’t be able to see the app until I unlocked it. Dang. Back to Google. After a hardcore montage of me googling, I found a tool in the Android SDK called monkeyrunner. This can be used to send swipes, touches, button presses, ect to an ADB enabled Android device. Awesome, but I really didn’t feel like scripting the swipes for my pattern lock. So I disabled it using the following:
su
sqlite3 /data/data/com.android.providers.settings/databases/settings.db "update system set value=0 where name='lock_pattern_autolock'"
sqlite3 /data/data/com.android.providers.settings/databases/settings.db "update system set value=0 where name='lockscreen.lockedoutpermanently'"
rm /data/system/gesture.key
sync
reboot
Now that the pattern lock was maimed, you could do any pattern and it will unlock the phone. So I wrote a quick monkeyrunner script that did just that:
start = (400, 700)
end = (500, 700)
device.drag(start, end, 0.2, 2)
Yeah! My screen unlocked and revealed the droid VNC Server app’s main screen. Now all I needed to do was hit the start button and with monkey runner that wasn’t a problem:
device.touch(300, 200, 'DOWN_AND_UP')
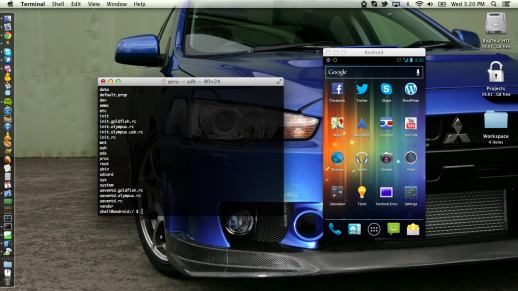
BAM! Good News Everyone! The sever fired up! Once the server was started, I was able to make things permanent by toggling the daemon to run on system boot. Now I can simply point a VNC viewer at the phone’s IP and use it to answer phone calls and read texts until I get a new phone or try replacing the screen again (shutter).
Dropped my atrix the other day which resulted in a very cracked touch panel. Fortunately it still worked if you could forgive the cracks all over the image. So I did what any normal geek would do and I ordered a new screen off of eBay and patiently awaited its arrival.